Cyber Threat Intelligence Meets Geopolitics: Global Watch for Security Teams
Most cyber threat intelligence platforms show you indicators of compromise in isolation: IP addresses, file hashes, domain names. They tell you what’s attacking, but not why.
When a wave of phishing campaigns targets European energy companies, is it financially motivated or state-sponsored? When a country’s internet goes dark, is it an infrastructure failure or a government-ordered shutdown? When botnet command-and-control servers cluster in a specific region, does it correlate with the geopolitical situation there?
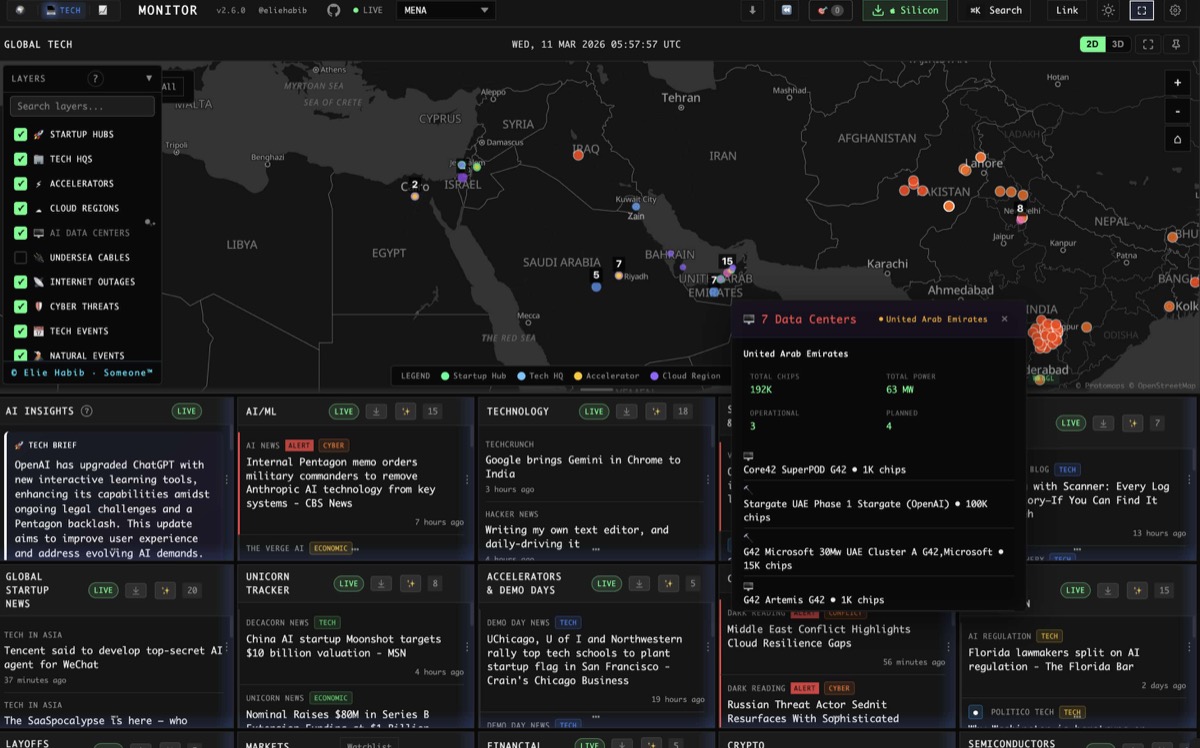
Global Watch answers these questions by putting cyber threat data on the same map as military movements, political instability scores, and infrastructure networks.
Integrated Threat Feeds
Feodo Tracker (abuse.ch)
The Feodo Tracker identifies active botnet command-and-control (C2) servers used by major banking trojans and malware families including Emotet, Dridex, TrickBot, and QakBot.
Global Watch maps these C2 servers geographically, showing:
- Active C2 server locations
- Malware family association
- Server hosting details
- First seen and last seen timestamps
When C2 servers cluster in a country whose CII (Country Instability Index) is rising, it may indicate state tolerance or state sponsorship of cybercrime during periods of geopolitical tension.
URLhaus (abuse.ch)
URLhaus tracks URLs distributing malware. Global Watch integrates this feed to show:
- Active malware distribution URLs by geography
- Payload types being distributed
- Hosting infrastructure patterns
- Takedown status and timeline
AlienVault OTX (Open Threat Exchange)
The Open Threat Exchange is a community-driven threat intelligence platform. Global Watch pulls curated “pulses” (collections of indicators) to show:
- Emerging attack campaigns
- Geographic targeting patterns
- Associated threat actor profiles
- Related indicators of compromise
AbuseIPDB
IP reputation data showing addresses associated with brute force attacks, spam, and other malicious activity.
C2IntelFeeds
Additional command-and-control intelligence feeds providing broader coverage of active C2 infrastructure across malware families.
Internet Outage Detection (Cloudflare Radar)
Global Watch integrates Cloudflare Radar data to detect and map internet outages globally. This reveals:
- Government-ordered shutdowns during protests or elections
- Infrastructure failures from natural disasters or attacks
- Submarine cable cuts affecting regional connectivity
- BGP hijacking incidents redirecting traffic through unauthorized networks
Mapping outages alongside conflict and protest data creates a powerful correlation: when a country’s internet goes dark the same day CII spikes and Telegram OSINT reports protests, the pattern is clear.
The Cyber Threat Map Layer
Toggle the cyber threat layer on Global Watch’s globe and you see a geospatial view of active threats:
- Red markers for C2 servers
- Orange markers for malware distribution URLs
- Yellow markers for threat intelligence pulses
- Gray overlays for internet outage zones
Zoom into a region and the density of threats becomes visible. Pan out and you see global attack patterns. Overlay the military bases layer and you might notice C2 infrastructure clustering near military installations. Overlay the undersea cable layer and see how outages align with physical infrastructure routes.
Geopolitical Context for Cyber Events
This is Global Watch’s unique contribution to threat intelligence. Here’s what the geopolitical layers add:
Attribution Context
When a new attack campaign targets NATO-aligned countries, Global Watch shows:
- Which strategic theaters are currently elevated
- Whether the targeted countries have rising CII scores
- Active military exercises or deployments in the region
- Recent diplomatic events that may have triggered the campaign
This doesn’t prove attribution, but it provides the context that threat analysts need for informed assessment.
Infrastructure Risk Assessment
Global Watch maps the critical infrastructure that cyber attacks target:
- Undersea cables carrying 95% of intercontinental internet traffic
- Pipelines with SCADA systems vulnerable to cyber-physical attacks
- Nuclear facilities with safety-critical control systems
- Financial centers processing trillions in daily transactions
- AI datacenters hosting critical AI infrastructure
When you overlay cyber threat data on infrastructure, you see the attack surface visually. A cluster of C2 servers in a country adjacent to undersea cable landing stations raises different concerns than the same cluster in an isolated interior region.
Predictive Indicators
Historically, cyber operations precede kinetic military action. The 2022 Ukraine conflict was preceded by months of cyber attacks against government and infrastructure targets. Global Watch’s combined view lets you watch for:
- Cyber threat spikes in countries with rising CII scores
- New C2 infrastructure deployment near strategic theaters
- Internet outage patterns that suggest preparation for information control
- Malware campaigns targeting specific national infrastructure
Practical Workflows for SOC Teams
Daily Threat Briefing
- Open Global Watch and check the cyber threat layer
- Review new C2 servers and malware URLs from the past 24 hours
- Cross-reference geographic distribution with the CII heatmap
- Check internet outage overlay for any new blackouts
- Read the AI-generated World Brief for geopolitical context
- Set keyword monitors for specific threat actor names or malware families
Incident Contextualization
When responding to an attack:
- Map the attack infrastructure on Global Watch
- Check if the source country’s CII has been rising
- Review if the target aligns with active strategic theaters
- Check Telegram OSINT for any related chatter
- Assess if physical infrastructure near the attack is at risk
- Generate an AI brief combining cyber and geopolitical indicators
Threat Hunting
- Filter cyber threat layer by specific malware family
- Identify geographic patterns in C2 infrastructure
- Correlate with news panel for recent geopolitical events in those regions
- Check prediction markets for escalation probabilities
- Monitor for infrastructure cascade effects if attacks succeed
Why Geopolitical Context Matters for Cybersecurity
The cybersecurity industry has spent two decades building tools that analyze threats in isolation. IP addresses, file hashes, and YARA rules are essential, but they exist in a vacuum without geopolitical context.
Consider two scenarios:
Scenario A: A new botnet C2 server appears in Country X. Your threat intel platform flags it. You block the IP. Move on.
Scenario B: A new botnet C2 server appears in Country X. Global Watch shows that Country X’s CII has spiked 15 points in a week. The strategic theater assessment shows elevated posture. ADS-B tracking shows unusual military flights. News velocity for the region has tripled. Telegram OSINT reports government mobilization.
Same C2 server. Dramatically different risk assessment. In Scenario B, that server might be part of a state-sponsored operation preceding military action. Your response should be proportionally different.
Global Watch doesn’t replace your SIEM, your EDR, or your threat intelligence platform. It adds the context layer that tells you why threats are happening and what might come next.
Add geopolitical context to your threat intelligence at globalwatch.vercel.app. Free, open source, and integrated with the intelligence data that matters.